Cybersecurity finally got near to the attention level it deserves during the pandemic lockdowns in many countries. A previous article on cybersecurity flagged up some service providers that work with larger companies through crowdsourcing the expertise required to deliver ethical hacking and penetration testing, and complete bug bounty programs. These providers include Bugcrowd, Synack and Crowdswarm.
The enormous numbers of people working remotely from home through residential broadband connections or domestic wifi setups were in many instances operating outside company security arrangements, which for many will continue indefinitely. It puts both employers and employees at greater risk of being compromised. Many local retailers quickly ramped up their ecommerce offerings with perhaps less than totally secure connections, endangering themselves and their online customers.
Hackers can pick on any business, large or small, whether for attempted financial gain or just for kicks. Larger companies have usually at least identified potential cybercrime threats, though smaller businesses were often left wondering what to do.
Adding a face to the crowd providing cybersecurity
Intigriti is another crowdsourced option for any business that does not have its own in-house dedicated resources. Intigriti describe a company’s IT operation as a “playground for ethical hackers, based on mutual trust.” They have recruited and vetted those ethical hackers to provide businesses with access to a reliable and trustworthy community of online security experts. They can be engaged on specific projects or on an on-going basis to continually test a system’s resilience. Responding to challenges stimulates them as much as a financial reward.
If you think you have a picture in your mind of an ethical hacker, Intigriti’s top hacker in the first half of 2020 is a 38  year old, Australian father of three. He operates under the pseudonym pudsec, and grew up dismantling and then rebuilding home computers. While doing this he came across and fixed many bugs, though under-estimated the extent and the value of the knowledge he had acquired until he began watching videos about other bug-hunters. Today he works as a full time Linux system administrator and Python/PHP software developer, and hunts down bugs as a hobby. With three children, his time is at a premium, and he’s looking into ways to automate some of the work while he’s away from his computer.
year old, Australian father of three. He operates under the pseudonym pudsec, and grew up dismantling and then rebuilding home computers. While doing this he came across and fixed many bugs, though under-estimated the extent and the value of the knowledge he had acquired until he began watching videos about other bug-hunters. Today he works as a full time Linux system administrator and Python/PHP software developer, and hunts down bugs as a hobby. With three children, his time is at a premium, and he’s looking into ways to automate some of the work while he’s away from his computer.
It’s definitely a collaborative activity among an active online community, with ethical hackers happily sharing advice and findings. “Twitter is an amazing resource for write-ups, PoCs, guides etc, there are heaps of bug hunters and researchers out there sharing vital information. I like to read as many tweets as I can but any write-ups will be added to my Pocket for later consumption, however the backlog is huge at the moment, I just need to work out the hacking/reading life balance which is tough.”
Many small businesses feel excluded
The opportunity to tap into skills and experience of ethical hackers such as pudsec on a crowdsourcing basis is an enormous benefit for any business whose system is able to provide him, and others like him, with a satisfying challenge.
However, many non-tech-minded small business owners feel themselves operating in almost a parallel universe alongside the ones that “get the tech.” To paraphrase United States Secretary of Defense Donald Rumsfeld, they don’t know what it is that they don’t know. Cybercrime exists, but the warning signs to look out for, or measures to put in place to prevent it happening, are beyond their knowledge and experience.
A new UK cybercrime initiative crowdsourced opinions from small and medium size business owners and operators to establish the scope of a number of critical issues.
Who can they go to for help? Specialists in this field speak an impenetrable language they don’t understand. It is an unregulated sector where there is no acknowledged benchmark or approved status of competency that cybersecurity firms have to meet, and no formal qualifications are required for individuals to operate. If a hack has already occurred, who should victims report it to?
A search for small business solutions
The UK’s solution is to create a network of not for profit Cyber Resilience Centres, inspired by the Founder of BRIM, Business Resilience International Management, a private consultancy that advises law enforcement to establish and develop a trusted contact point for SMEs (small and medium sized enterprises). The self-managing CRCs will each develop their own community of members, and the required service providers will come only from within those members in a mutually beneficial relationship.
Entry-level membership is available free of charge to encourage as many businesses as possible to become involved, and beyond that a price-tiered membership scheme will qualify members for both access to additional services, and opportunities to take on a range of defined roles. Required services will be provided to members by members.
The Board of each CRC will be made up of companies that operate in the IT sector and can provide relevant skills and expertise, and they will pay a fee of £10,000. A proportion of this may be payable through providing services to members. This enables businesses to use spare capacity to financial advantage, just as an Airbnb host is able to gain from letting out a spare room, or an Uber driver for giving someone a ride in their car. The Boards will oversee matters of legal governance and crucial decision-making.
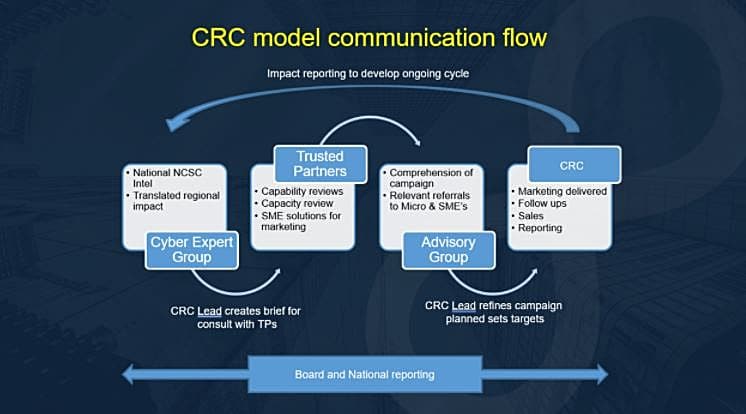
A branch of the UK’s GCHQ international intelligence monitoring unit, along with regional police forces, will liaise with each Centre to provide intelligence on trends and developments in related criminal activities that individual local businesses would otherwise never be aware of. Fee paying members with the required experience and knowledge will make up a Cyber Expert Group to interpret this information, and work with police advisers to determine related best practices.
Representative cross-sections of each CRC’s fee-paying members will form Action Groups. Their role is to represent the opinions of all the members and keep the deliverables relevant. Members will thus be able to actively co-create the agenda of their CRC to tailor it to their particular regional business environment.
In the style of a talent accelerator hub, day-to-day requests for services will be fed to a network of recent graduates who will operate under the mentorship of experienced consultant members. The members commissioning the work will be briefed on the sector’s jargon so that they understand what’s being said and done, and can grade the quality of the response they receive. The work will be performed to a uniform standard and at set prices, so everyone pays the same and receives the same. Each graduate will work for one to two years in this role, which will speed up their development and build a pipeline of future talent.
When a member has more serious requirements, each CRC will have a Trusted Partner List of member companies that can provide what’s needed.
This collaborative, community-building structure with its repeated theme at each stage of “for the members, by the members” has already received considerable international interest. Any queries and questions can be directed to BRIM’s Director of Programmes, [email protected].




0 Comments